by Maria Florio | Sep 24, 2013 | Blog
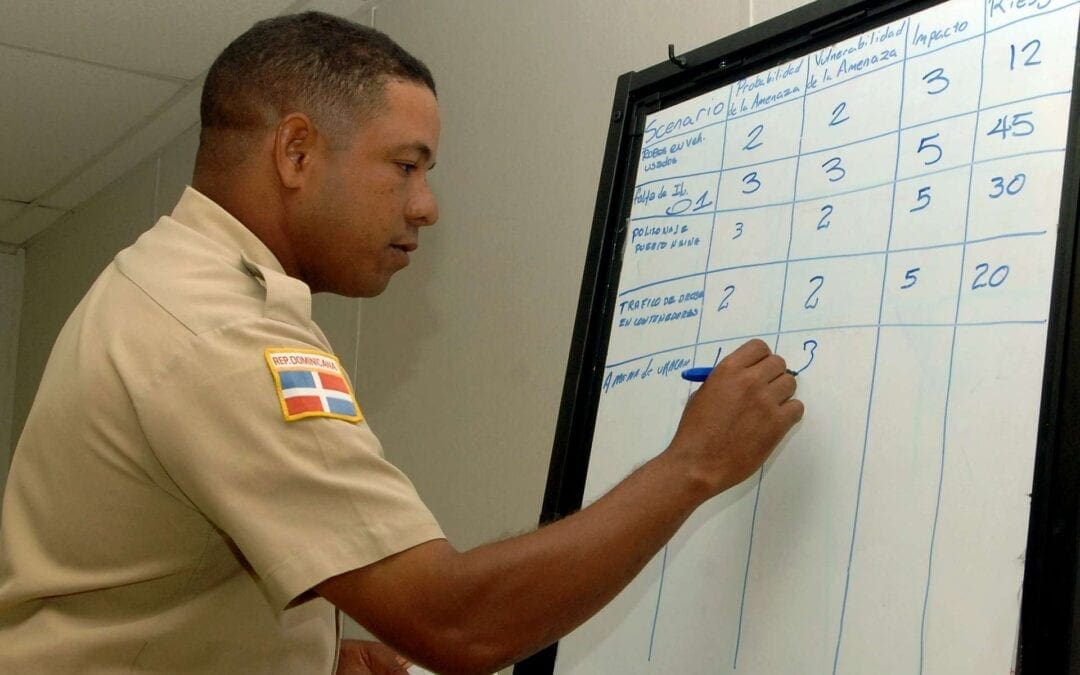
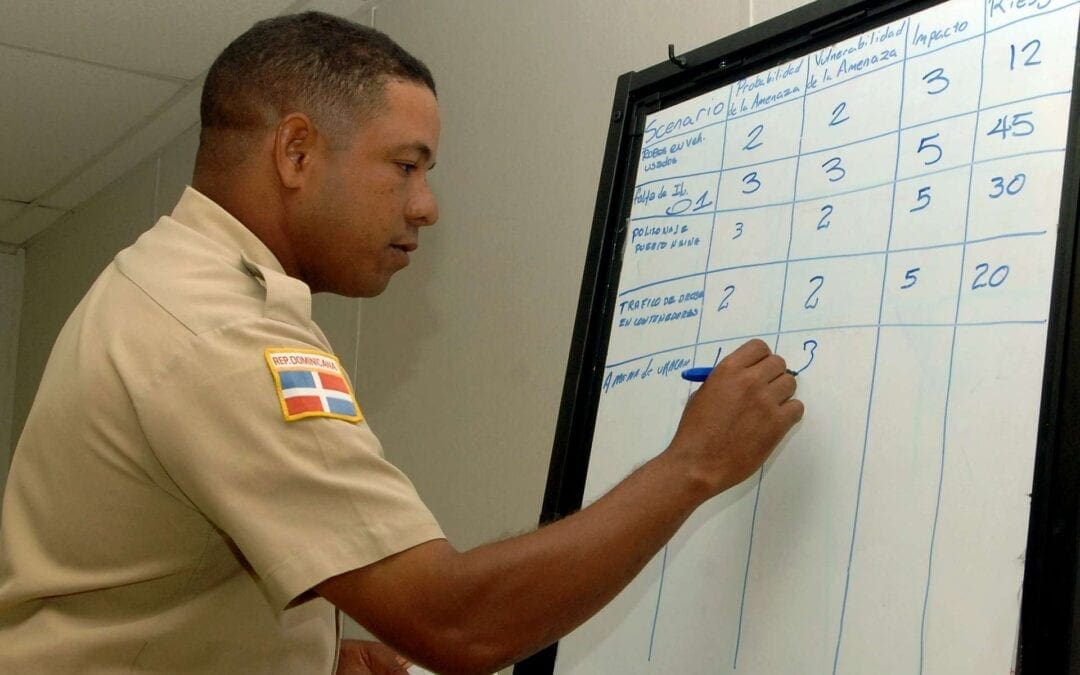
A recent study focusing on the state of risk-based security management has found that only 46 percent of IT professionals have deployed continuous monitoring. Furthermore, many organizations that spend on perceived security risks, have not implemented preventive security technologies, and do not use audits often to identify security risks.
by Maria Florio | Sep 4, 2013 | Blog
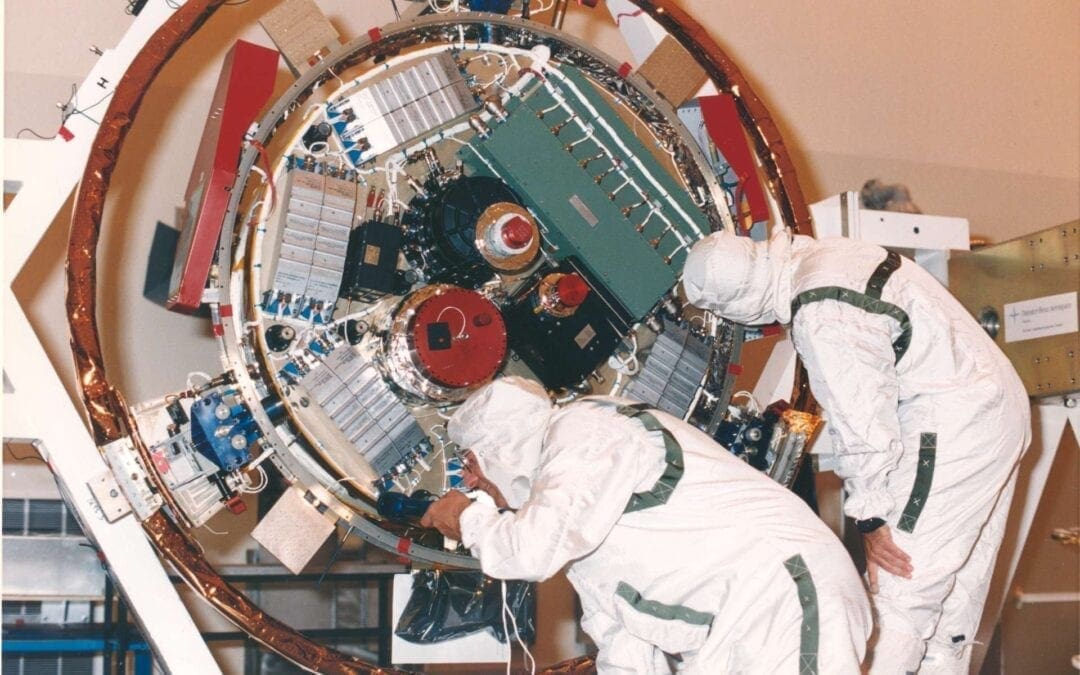
In today’s marketplace the most valuable aspect of an organization, and sometimes the only things of value, is the information created, stored, and used to serve their customers and to be able to maintain a competitive advantage over their competitors. Many organizations have realized this and have allocated budget to systems to protect this data. The challenge is this only addresses one-third of the picture.
by Maria Florio | Aug 28, 2013 | Blog
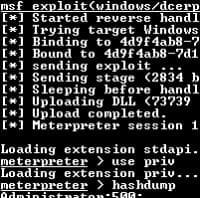
As networks expand and evolve, so do the attack vectors and the need to ensure you do not have any gaps in your network. Furthermore, virtual environments have increased due to the fact that most IT groups have been asked to do more with less. This request comes at a price and IT professionals are worried about the protection of their information assets. Solomon recommends three ways to help reduce and address these concerns.

by Maria Florio | Aug 21, 2013 | Blog
One of the best ways to check the security of your web-based applications is to check the Open Web Security Application Project (OWASP) Top 10 List. The OWASP has been the basis for a security checklist for ten years now. Did you know the OWASP updated their Top 10 list this year? How often do you look for the Top 10 risks in your web-based applications?

by Maria Florio | Aug 19, 2013 | Blog
The CIO is in charge of various information security areas; this can make it challenging to ensure top security and compliance are met at all times. The challenge doesn’t arise from any lack on the part of the CIO, but it arises from the limited time and resources available to them.