The Due Diligence Playbook You Used Six Months Ago May Already Be Outdated
Last updated:
Last week, the Cloud Security Alliance, SANS Institute, and OWASP published a joint strategy briefing called “The AI Vulnerability Storm.” The authors include some of the most respected names in cybersecurity. Former CISA Director Jen Easterly. Bruce Schneier. Google’s CISO. The former NSA Cybersecurity Director. Dozens more.
The report was written for CISOs. But if you are a PE partner, a deal team lead, or anyone responsible for evaluating risk in an acquisition, you need to read it through a different lens.
Because Glasswing did not just change cybersecurity. It changed cyber due diligence.
The Old Playbook
Most cyber due diligence in M&A follows a familiar pattern. Review the target’s security policies. Check for basic controls. Look at their last penetration test. Maybe run an outside-in scan. Ask whether they have cyber insurance. Check a few boxes.
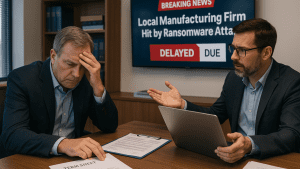
That approach was already thin. But it worked well enough when the threat landscape moved at a predictable pace. You had time. If something was missed, there was usually a window to find it and fix it after close.
That window just closed.
And even before it closed, the old playbook was already costing real money. Research from FTI Consulting’s CISO Redefined III report in March 2026 puts numbers on what happens when cyber diligence is treated as a checkbox: 20% of deals are delayed or paused, 42% see significant value reductions, and 58% end with impaired post-close financial targets. Cyber has been ranked the number one business and financial risk in the world for the fifth year running by the Allianz Risk Barometer.
Those numbers were bad enough before Glasswing. They are about to get worse for anyone still running the old playbook.
What Changed
The Glasswing report documents a fundamental shift in deal risk: AI has collapsed the time between a vulnerability’s discovery and its use in an attack. The data shows this window dropping from over two years in 2018 to less than one day in 2026.
Let that settle for a moment. Less than one day.
That means a target company sitting on unpatched vulnerabilities is no longer carrying theoretical risk. They are carrying immediate risk. And if they do not know what vulnerabilities exist in their environment, in their own code, in their third-party software, in their vendor relationships, then neither do you.
You cannot price what you cannot see.
Six Ways This Changes Due Diligence
The checklist is not enough anymore. Asking a target, “Do you have endpoint protection?” or “When was your last pen test?” tells you what they bought. It does not tell you whether it works. When attackers can discover and exploit vulnerabilities in hours, the question is no longer “what controls do you have?” It is “Can you prove those controls work at the speed the threat now moves?” That is a fundamentally different question, and most targets cannot answer it.
Risk models in deal valuations may be understated. If the assumptions baked into your cyber risk assessment are based on pre-AI timelines for exploitation, incident frequency, and attack complexity, then the risk component in your deal model may not reflect reality. You may be pricing risk that does not exist anymore and missing risk that does. The report explicitly warns that security reporting metrics built on these old assumptions could lead to inaccurate business projections. That is not just a security problem. That is a valuation problem.
Vendor and supply chain risk matters more than ever. The report notes that Glasswing gave roughly 40 major software vendors early access to find and patch their own vulnerabilities. That means a wave of critical patches is coming. For any target you are evaluating, the question becomes: how dependent are they on third-party software, and can they actually deploy patches at the pace this environment demands? A target with deep dependencies and slow vendor relationships carries a risk that will show up after close.
The standard of “reasonable” is shifting. The report raises an important regulatory point. The EU AI Act takes effect in August 2026. Existing regulations already use reasonableness as a legal test. When AI tools that find vulnerabilities become widely available and affordable, the bar for what counts as reasonable defensive effort moves. Boards and acquirers will face questions about whether they used available tools. Whether they scanned their own systems. Whether not doing so was negligent. That is a liability question that belongs in every deal review.
Your MSP is now an attack vector, not just a service provider. This is the one most deal teams overlook entirely. The report warns about supply chain risk and vendor dependencies, and there is no vendor with deeper access to a company’s environment than their managed service provider. MSPs hold privileged credentials. They have remote access to servers, endpoints, and cloud infrastructure. In many cases they are the de facto IT department. In the Glasswing world, where vulnerabilities are discovered and exploited in hours, a compromised MSP is not one company’s problem. It is every client they touch. When you are evaluating a target, you are not just evaluating their security. You are inheriting the security posture of every vendor with keys to their environment. And the MSP is usually holding the biggest set of keys.
Trust without validation is how deals blow up. Here is the part I see over and over. A target fills out a security questionnaire about themselves. Their internal IT team says everything is fine. Their MSP confirms it. The buyer reviews it. Everyone feels good.
But stop and think about what just happened. You asked the people who built and manage the environment to tell you whether their own work is secure. That is like asking your bookkeeper to audit their own books.
It is not a question of honesty. It is a question of structure. No PE firm would accept a target’s internal accountant signing off on their own financials during diligence. You bring in an independent auditor. That is not optional. It is how you get trustworthy results.
Cyber due diligence should work the same way. The MSP and internal IT do the day to day work. That is their job and it is important work. But they cannot independently validate their own security posture. They are too close to it. They have blind spots built into the way they operate. And now, in a world where AI is finding and exploiting vulnerabilities faster than most teams can even inventory their systems, those blind spots carry real financial consequences.
Cyber risk is not about what you think or feel. It is about what you can prove. And proof requires independence.
What to Do About It
The good news is that the same AI capabilities creating this risk also create an opportunity for buyers willing to use them.
You can now scan a target’s codebase and environment for vulnerabilities at a speed and depth that was not possible a year ago. You can validate whether their controls actually work, not just whether they exist on paper. You can assess their patching velocity, their incident response readiness, and their vendor risk posture against the timeline the threat now operates on.
But that validation has to come from someone who did not build the environment, does not manage it, and does not have a financial relationship that depends on telling you everything is fine.
The right questions are no longer about checkboxes. They are about proof. And proof requires independence.
Before your next deal, ask:
Who is validating the target’s security posture, and are they independent from the people who built and manage the environment?
Can the target prove their security controls work at the speed the current threat demands, or are they reporting based on assumptions that predate this shift?
How much privileged access does the target’s MSP have, and what is that MSP’s own security posture?
Do they know what vulnerabilities exist in their own code and third-party dependencies right now, not six months ago?
Can they handle a surge of critical patches from multiple vendors in the same week without disrupting operations?
What would this deal look like if a major vulnerability were exploited in the first 90 days after close?
That last question is the one most deal teams never ask. In the current environment, it may be the most important one.
The Bottom Line
The due diligence playbook that worked six months ago was built for a world where you had time to find problems and fix them. That world is gone.
But here is what the data also shows. When cyber gets the same independent, pre-marketing rigor we already give Quality of Earnings, tax, and litigation risk, the numbers improve dramatically. Deal delays drop from 20% to the 5 to 8% range. Significant value reductions decline from 42% to 15 to 22%. Post close impairments fall from 58% to 8 to 15%. The deal process actually accelerates. Seller proceeds are materially protected.
That is not a cybersecurity initiative. That is a deal outcome improvement.
Glasswing did not create this shift. AI-driven vulnerability discovery has been accelerating for over a year. But Glasswing made it impossible to ignore. It landed in boardrooms. It made headlines beyond the security community. And it established a public record that this capability exists and is available.
Which means every deal from here forward carries an implicit question: Did you account for this?
The organizations and the investors who get ahead of this will be the ones who stop treating cyber due diligence as a compliance exercise and start treating it as what it actually is.
A financial decision based on provable risk.
Mike Fitzpatrick is the Founder and CEO of NCX Group, an independent cyber risk advisory firm that helps CEOs, CFOs, private equity firms, and M&A deal teams understand, validate, and manage cyber risk in financial and operational terms. He is a Distinguished Fellow at the Ponemon Institute and Cyber Risk Leadership Content Partner for CEO Zones.
Repost from LinkedIn – Read the original article on LinkedIn